Business Continuity Management / Disaster Recovery , Critical Infrastructure Security , Cybercrime
Ukrainian Websites Defaced as Tensions With Russia Continue
'Mass Hacking Attack' Leaves Threatening Messages on Government and Embassy Sites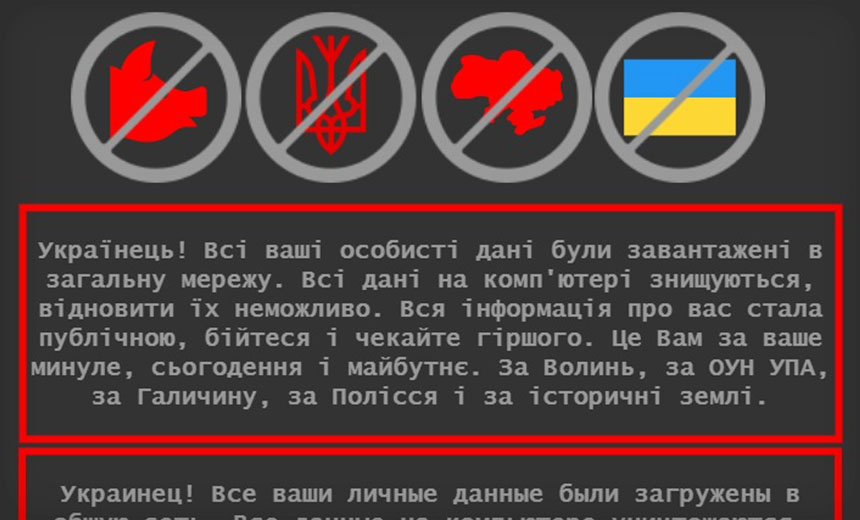
Multiple Ukrainian websites were defaced late Thursday and early Friday with warnings to "be afraid and expect the worst," as Russian troops remain massed on the country's border.
See Also: Modernizing Malware Security with Cloud Sandboxing in the Public Sector
Affected government websites have been taken offline while they get restored.
"As a result of a mass hacking attack, the website of the Foreign Ministry of Ukraine and a number of other state authorities are temporarily out of order," says Oleg Nikolenko, a spokesman for Ukraine's Ministry of Foreign Affairs. The site for the Ministry of Education and Science was among the other government websites that were defaced.
Websites for the Swedish, U.K. and U.S. embassies in Ukraine were also defaced, the BBC reported. As of Friday morning, the Swedish and U.S. sites had been restored, but the website for Britain's embassy in Ukraine's capital city of Kyiv remained offline.
The defaced websites included messages written in Ukrainian, Russian and Polish. The messages claimed that all of the data on the website had been stolen, before the site had been wiped and made unrecoverable.
"All information about you has become public, be careful and expect the worst. This is for your past, present and future," messages on the defaced sites read.
As a result of a massive cyber attack, the websites of the Ministry of Foreign Affairs and a number of other government agencies are temporarily down. Our specialists have already started restoring the work of IT systems, and the cyberpolice has opened an investigation.
— Oleg Nikolenko (@OlegNikolenko_) January 14, 2022
Some of the Ukrainian government websites have already been restored and the rest "will be operating soon," says the Security Service of Ukraine, or SBU, which has launched a criminal investigation into the matter.
"To prevent the attack from spreading to other resources and to localize the technical problem, a number of other government websites have been suspended," it says.
Ukraine's computer emergency response team, CERT-UA, reports that all of the defaced government sites may have used the same content management system: October CMS Specifically, it suspects that the attackers exploited a vulnerability in October that was the subject of an Aug. 26, 2021, security alert that recommended users upgrade to a newer, patched version of the software, or apply a specified workaround.
Contrary to what the messaging posted to the defaced sites claimed, the SBU says that its preliminary investigation has found that no data being stored on the sites appears to have been tampered with, and that "no leakage of personal data occurred."
The Ukrainian government has not attributed the defacements to any particular individual or government. "It's too early to draw conclusions, but there is a long record of Russian assaults against Ukraine in the past," a foreign ministry spokesman told Reuters.
Threat From Russia
Last month, Russia moved 175,000 soldiers to its border with Ukraine, as Russian President Vladimir Putin continued to criticize Ukraine's plans to join NATO.
The White House last month warned that Moscow was running disinformation campaigns targeting Ukraine President Volodymyr Zelenskyy's administration and others.
Cybersecurity experts have also reported seeing a massive increase in online attacks against Ukrainian targets (see: Cyber Activity Surges as Russia Masses on Ukraine's Border).
Russian Troops Remain Massed
The defacements have occurred after a week of diplomatic discussions between NATO and Russia.
According to Western intelligence officials, Russia continues to maintain deployments of about 100,000 troops on its border with Ukraine and in territory it's occupied in eastern Ukraine, which it invaded in 2014.
President Vladimir Putin threatened to further invade Ukraine if the country is allowed to join NATO. But the U.S. and its NATO allies said Ukraine's decision is not open to negotiation, and have called on Moscow to de-escalate and pursue diplomacy, threatening that there will be reprisals for any further military activity.
Week of Intensive Diplomacy Wraps
White House National Security Adviser Jake Sullivan told reporters Thursday that after "an intensive week of diplomacy in multiple formats," Moscow had as yet scheduled no further talks, and no agreement had been reached.
He emphasized that a key part of further negotiations would involve Russia "reducing the number of forces that they have deployed in aggressive postures towards Ukraine," and said Moscow's call for Ukraine to drop its bid for NATO membership was among a list of "non-starters" for discussion.
As yet, however, Moscow shows no signs of backing down. On Tuesday, Russia's military conducted live-fire exercises on Ukraine's border. On Wednesday, Russian Deputy Foreign Minister Alexander Grushko told state-owned RIA Novosti that any expansion of NATO would pose serious risks to Russia's national security. He also warned that if talks failed, Russia might use military force to deal with any perceived security threats.
Sullivan said it's not clear what Putin will do next, but that the U.S. and allies stand ready to impose serious sanctions and other measures.
"The United States and our allies and partners are prepared for any contingency, any eventuality," he said. "We're prepared to keep moving forward down the diplomatic path in good faith, and we're prepared to respond if Russia acts. And beyond that, all we can do is get ready, and we are ready."
'Russian State-Sponsored Cyber Threats'
This week, the U.S. and U.K. issued alerts warning domestic businesses to beware of Russian activity targeting critical infrastructure.
Intelligence officials say Russia has a history of prepositioning attack code that it can later use to support its strategic or military aims. The country also hasn't hesitated to experiment with such tactics, for example, by crashing power generation systems in Ukraine in the dead of winter in both 2015 and 2016.
The U.S. warning was issued in the form of a Tuesday joint advisory from the Cybersecurity and Infrastructure Security Agency, National Security Agency and FBI.
"CISA, the FBI, and NSA encourage the cybersecurity community - especially critical infrastructure network defenders - to adopt a heightened state of awareness and to conduct proactive threat hunting," it said. The advisory included details of vulnerabilities being targeted by advanced persistent threat groups that it recommended be immediately patched if they had not been patched already. It also urged all organizations to install all updates, prioritized by severity, as soon as possible, to ensure they had robust antivirus software and to use multifactor authentication as widely as possible.
On Wednesday, Britain's National Cyber Security Center called on the U.K. to follow the U.S. advice.
"The NCSC recommends that organizations follow the advice set out within the advisory, which also lists 13 vulnerabilities known to have been exploited by Russian-backed actors in order to gain access to networks, and warns that actors have also used spear-phishing and brute force techniques successfully," it said.
The advisories are clearly linked to the tensions between Russia and Ukraine, and by extension the threat posed to NATO members, says Adam Flatley, a member of the U.S. Ransomware Task Force who formerly served as a technical lead for the NSA, and who's now director of threat intelligence for a company called Redacted.
"It will be important for U.S. organizations, especially the critical infrastructure vertical, to pay extra attention to cybersecurity in order to mitigate Russia's retaliatory options, should the U.S. 'act decisively' in response to an invasion as the Biden administration has promised," he said.
Updates: Added information from CERT-UA.