Sponsored by MetricStream
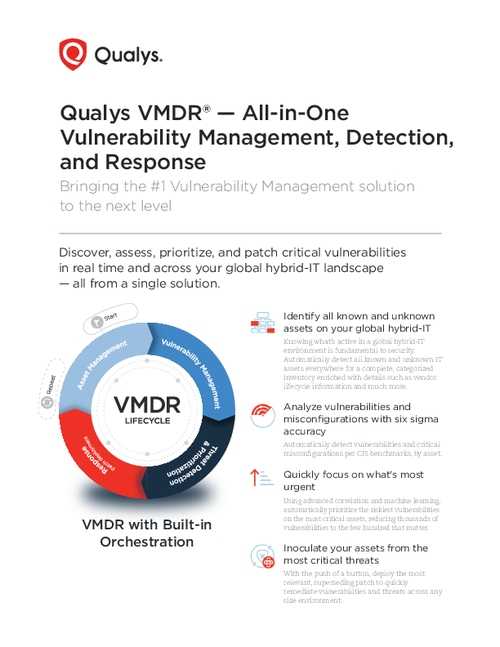
Sponsored by Qualys Inc.
VMDR: All-in-One Vulnerability Management, Detection & Response
Sponsored by Qualys Inc.
An All-in-One Vulnerability Management, Detection, and Response Solution
Sponsored by Verizon
Mobile Security Index 2021
Sponsored by Cyberark
5 Ways to Rapidly Reduce Risk
Sponsored by Proofpoint
2020 Cost of Insider Threats: Global Report
Sponsored by Nozomi Networks
Case Study: Global Pharma Expands OT Visibility and Strengthens Security
Sponsored by Proofpoint
2020 User Risk Report
Sponsored by IBM
Forrester Wave: Risk-Based Authentication, Q2 2020
Sponsored by IBM
Assessing cyber risk in M&A
Sponsored by Okta
Leveraging Identity Data in Cyber Attack Detection and Response
Sponsored by OneSpan
eIDAS and E-Signature: A Legal Perspective
Sponsored by Rapid7